In the autumn of 2020, Kaspersky researchers identified two APT incidents that targeted entities related to COVID-19 research – a Ministry of Health body and a pharmaceutical company. Kaspersky experts assessed with high confidence that the activities can be attributed to the infamous Lazarus group.
As the pandemic and restrictive measures across the world continue, many parties involved are trying to speed up vaccine development by any means available. While most of the work is well intentioned, there is another side to this coin as some threat actors are trying to capitalize on this for their own gain. As they continue to track the Lazarus group’s ongoing campaigns targeting various industries, Kaspersky experts have discovered that the actor went after COVID-19-related entities just a couple of months ago. Namely, two incidents were identified.
The first one was an attack against a Ministry of Health body. Two Windows servers in the organization were compromised with sophisticated malware on October 27, 2020. The malware used is known by Kaspersky, named ‘wAgent’. Closer analysis has shown that the wAgent malware used against the Ministry of Health has the same infection scheme as the malware Lazarus group previously used in attacks on cryptocurrency businesses.
The second incident involved a pharmaceutical company. According to Kaspersky telemetry, the company was breached on September 25, 2020. This company is developing a COVID-19 vaccine and is also authorized to produce and distribute it. This time, the attacker deployed the Bookcode malware, previously reported by a security vendor to be connected to Lazarus, in a supply chain attack through a South Korean software company. Kaspersky researchers also witnessed Lazarus group carry out spear-phishing or strategically compromise websites in order to deliver Bookcode malware in the past.
Both wAgent and Bookcode malware, used in both attacks, have similar functionalities, such as a full-featured backdoor. After deploying the final payload, the malware operator can control a victim’s machine in nearly any manner they wish.
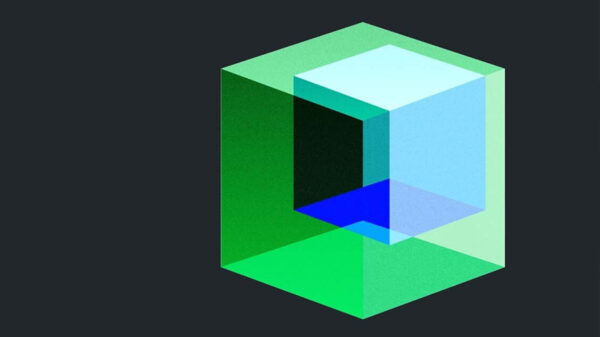
Relationship of recent Lazarus group attack
Given the noted overlaps, Kaspersky researchers confirm with high confidence that both incidents are connected to the Lazarus group. The research is still ongoing.
“These two incidents reveal Lazarus group’s interest in intelligence related to COVID-19. While the group is mostly known for its financial activities, it is a good reminder that it can go after strategic research as well. We believe that all entities currently involved in activities such as vaccine research or crisis handling should be on high alert for cyberattacks,” comments Seongsu Park, security expert at Kaspersky.
Kaspersky products detect the wAgent malware as HEUR:Trojan.Win32.Manuscrypt.gen and Trojan.Win64.Manuscrypt.bx.
The Bookcode malware is detected as Trojan.Win64.Manuscrypt.ce.
To stay safe from sophisticated threats, Kaspersky recommends taking the following security measures:
- Provide your SOC team with access to the latest threat intelligence (TI). The Kaspersky Threat Intelligence Portal grants access to the company’s TI, providing cyberattack data and insights gathered by Kaspersky for more than 20 years.
- Provide your staff with basic cybersecurity hygiene training, as many targeted attacks start with phishing or other social engineering techniques.
- Organizations that would like to conduct their own investigations will benefit from Kaspersky Threat Attribution Engine. It matches a discovered malicious code against malware databases, and, based on the code similarities, attributes it to previously revealed APT campaigns.
- For endpoint level detection, investigation and timely remediation of incidents, implement EDR solutions such as Kaspersky Endpoint Detection and Response.
- In addition to adopting essential endpoint protection, implement a corporate-grade security solution that detects advanced threats on the network level at an early stage, such as Kaspersky Anti Targeted Attack Platform.