Sophos, a global player in next-generation cybersecurity, published a report, “Maze Attackers Adopt Ragnar Locker Virtual Machine Technique,” which shows how attackers tried three different ways to execute Maze ransomware during a single attack while demanding a $15 million ransom.
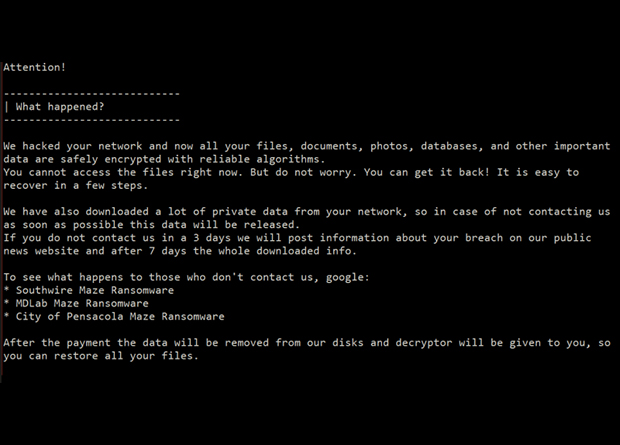
On the third try, the Maze operators attempted to leverage virtual machines (VM) to spread the ransomware, a technique pioneered by Ragnar Locker, as reported by Sophos in May 2020. Maze is one of the most notorious ransomware families, active since 2019 when it evolved from ChaCha ransomware, and it was among the first to combine data encryption with information theft.
How Maze’s Attack Attempts Unfolded
The investigation revealed that the attackers had penetrated the network at least six days before their first attempt to launch the ransomware payload. During this time, the attackers explored the network, ran legitimate third party tools, established connections, and exfiltrated data to a cloud storage service to prepare for the release of the ransomware component.
Upon launching the first ransomware attack, the operators demanded a $15 million ransom from the target of the attack. The target did not pay the ransom. When the attackers realized the first attack had failed, they launched a second, slightly different attempt. This was intercepted by security tools and the Sophos Managed Threat Response (MTR) team that was handling the incident response efforts. For the third attempt, the attackers used a reconfigured version of Ragnar Locker’s VM technique, this time running Windows 7 instead of Ragnar Locker’s Windows XP VM, and targeted just one file server. The attack and the Ragnar Locker technique were immediately recognized and blocked.
“The attack chain uncovered by Sophos threat responders highlights the agility of human adversaries and their ability to quickly substitute and reconfigure tools and return to the ring for another round,” said Peter Mackenzie, incident response manager, Sophos. “The use of a noisy Ragnar Locker virtual machine technique, with its big foot-print and CPU usage, could reflect a growing frustration on the part of the attackers after their first two attempts to encrypt data failed.”
Steps to Prevent Cyberattacks
Sophos recommends that to prevent cyberattacks, particularly ransomware, IT security teams need to reduce the attack surface by updating to cloud-based, layered security systems, including anti-ransomware technology, educate employees on what to look out for, and consider setting up or engaging a human threat hunting service to spot clues an active attack is underway.
“Every organization is a target, and any spam or phishing email, exposed RDP port, vulnerable exploitable gateway device or stolen remote access credentials provides enough of an entry point for adversaries to gain a foothold,” said Mackenzie.