By Jeff Castillo, Country Manager of Fortinet Philippines
This year, cloud computing is definitely poised to gain importance among enterprises. Chief Information Officers are now convinced that when properly implemented, cloud computing can dramatically improve a firm’s agility and productivity while cutting infrastructure cost. Companies large and small will move significant parts of their operations to the cloud in the next one to two years.
Yet while every organization wants a piece of the cloud action, not all of them will get the results they desire. Here are the top five mistakes to avoid:
1. Not opting for the right cloud model
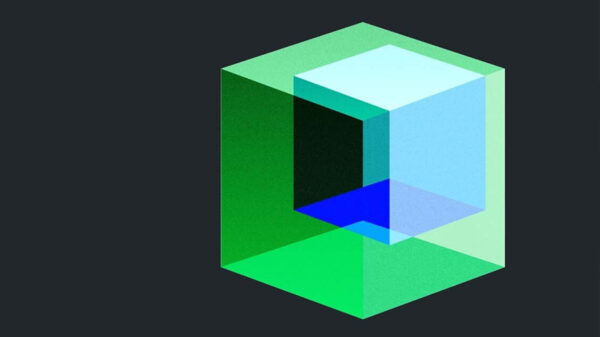
Companies moving to the cloud can choose from public clouds, private clouds, community clouds or hybrid clouds.
Public cloud: This is owned by a cloud provider and made available to the general public on a multi-tenant, pay-as-you-use basis.
Private cloud: This is owned and deployed by an organization for internal use as a single tenant.
Community cloud: This is cooperatively shared by a set of tenants, often from the same industry.
Hybrid cloud: This spans the cloud deployment models listed above, enabling applications and data to move easily from one cloud to the other.
Each type of cloud deployment offers its advantages. The factors to consider before adoption are the business criticality of the applications the firm wants to move to the cloud, regulatory issues, necessary service levels, usage patterns for the workloads and how integrated the application must be with other enterprise functions.
2. Not integrating cloud security into your corporate security policy
Your cloud security and corporate security policies must be integrated. Instead of creating a new security policy for the cloud, however, extend your existing security policies to accommodate this additional platform. To modify your policies for cloud, you need to consider similar factors: where the data is stored, how the data is protected, who has access to the data, compliance with regulations, and service level agreements.
When properly done, adoption of cloud computing can be an opportunity to improve your security policies and overall security posture.
3. Counting on the security of your cloud-based service provider
Do not assume that your data is automatically secure just because you use a service provider. You need to do a comprehensive review of the provider’s security technology and processes, and check how they secure your data and their infrastructure. Specifically, you should look into the following:
Application and data transportability: Does your provider allow you to export existing applications, data and processes into the cloud? Can you import these back just as easily?
Data center physical security: How does the service provider protect its physical data centers? Are they using SAS 70 Type II data centers, and how well trained and skilled are their data center operators?
Access and operations security: How does your provider control access to physical machines? Who is able to access these machines, and how are the machines managed?
Virtual data center security: Cloud architecture is key to efficiency. Find out how the individual pieces like the compute nodes, network nodes and storage nodes are architected, and how they are integrated and secured.
Application and data security: To implement your policies, the cloud solution must enable you to define groups, roles with granular role-based access control, proper password policies and data encryption (in transit and at rest).
4. Assuming that you are no longer responsible for securing data
Never think that outsourcing your applications or systems means you can abdicate responsibility for data breach. Some have this misconception but you must understand that your company is still ultimately accountable to customers and other stakeholders for the sanctity of your data. Simply put, it’s your CEO that risks going to jail, not the cloud provider’s.
5. Not knowing which local laws apply
Data that is secure in one country may not be secure in another. In many cases though, users of cloud services don’t know where their information is held. Currently in the process of harmonising the data laws of its member states, the European Union favours very strict protection of privacy, while in America, laws such as the US Patriot Act give government and other agencies virtually unlimited powers to access information belonging to companies.
Always know where your data is held. If necessary, store your data in more than one location. It is advisable to choose a jurisdiction where you will still have access to your data should your contract with the cloud provider be unexpectedly terminated. The service provider should also be able to give you flexibility on where you want your data to be held.
The bottom line is that the adoption of cloud technology must come with risk mitigation steps, and firms are well served to plan for and act on these steps from the outset, so that returns on their cloud investments can be maximized.